Now Sitecore PowerShell Extensions provides a User Account Control (UAC) feature akin to that of Microsoft Windows. Security is very important but can be annoying. An elevated session state is required to run the script. Each time when elevated session state expires then you will be prompt for credentials.

Fortunately, there are settings in the file ‘Cognifide.PowerShell.config’, where default settings can be changed. For me, the most inconvenience is that I need to edit the file. Sometimes I do not have access to the server but only to the Sitecore client. Powershell will help a little 🙂
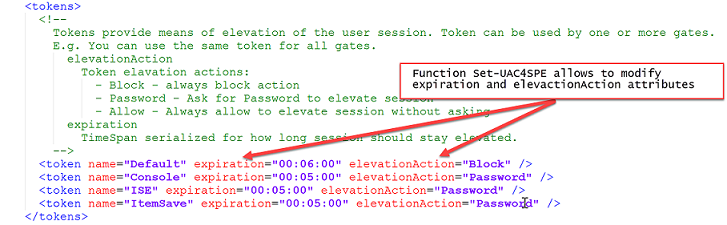
You can use this function to change default security settings. You can do this from a SPE console in Sitecore, but remember that this script will change a config file and Sitecore will be restarted.
# Session expires after 30 minutes
Set-UAC4SPE -Token ISE -Expiration '00:30:00'
| function Get-DefaultSpeConfig() | |
| { | |
| # $AppPath is SPE console variable, see Variables on https://doc.sitecorepowershell.com/interfaces.html | |
| if( $AppPath -ne $null ) | |
| { | |
| return Join-Path -Path $AppPath -ChildPath "App_Config\Include\Cognifide.PowerShell.config" | |
| } | |
| } | |
| function Set-UAC4SPE | |
| { | |
| <# | |
| .SYNOPSIS | |
| Sets an User Access Control parameters for Sitecore Powershell Extension | |
| .DESCRIPTION | |
| More about Sitecore Powershell Extension security https://doc.sitecorepowershell.com/security.html. | |
| This is part of https://bitbucket.org/sitecoreautomationteam/sitecore-automation/wiki/Home | |
| .PARAMETER Token | |
| An unique string used for the gate token attribute ('Default','Console','ISE','ItemSave') | |
| .PARAMETER Action | |
| An action to perform when session elevation is triggered (Allow, Block, Password) | |
| .PARAMETER Expiration | |
| A timespan used to determine the elevated session lifetime (hh:mm:ss) | |
| .PARAMETER SpeConfig | |
| A path to Cognifide.PowerShell.config. | |
| If this function is used in a SPE console then default parameter should be enough Get-DefaultSpeConfig | |
| .EXAMPLE | |
| Set-UAC4SPE -Token Console -Expiration '00:06:00' | |
| Set-UAC4SPE -Token Console -Expiration '00:06:00' -Action Allow | |
| .EXAMPLE | |
| PowerShell will number them for you when it displays your help text to a user. | |
| #> | |
| [CmdletBinding(SupportsShouldProcess=$true)] | |
| Param( | |
| [parameter(Mandatory=$true)] | |
| [ValidateSet('Default','Console','ISE','ItemSave')] | |
| [string]$Token = $null, | |
| [parameter()] | |
| [ValidateSet('Block','Password','Allow')] | |
| [string]$Action = $null, | |
| [string]$Expiration = $null, | |
| [string]$SpeConfig = (Get-DefaultSpeConfig) | |
| ) | |
| Write-Verbose "Set User Account Control in file $SpeConfig" | |
| [xml]$XmlDocument = Get-Content -Path $SpeConfig | |
| $xpath = "//configuration/sitecore/powershell/userAccountControl/tokens//token[@name = '$Token' ]" | |
| $tokenNode = $XmlDocument.SelectSingleNode($xpath) | |
| if( $Action -ne '' ) | |
| { | |
| $tokenNode.Attributes["elevationAction"].Value = $Action | |
| if ($pscmdlet.ShouldProcess("Set elevationAction to $Action on $SpeConfig")) | |
| { | |
| $XmlDocument.Save($SpeConfig) | |
| } | |
| } | |
| if( $Expiration -ne '' ) | |
| { | |
| $tokenNode.Attributes["expiration"].Value = $Expiration | |
| if ($pscmdlet.ShouldProcess("Set expiration to $Expiration on $SpeConfig")) | |
| { | |
| $XmlDocument.Save($SpeConfig) | |
| } | |
| } | |
| } |

1 comment